Sommaire: Deploying firewalls architecture firewall designs
Preface
Deploying Firewalls
1. Design the firewall system.
2. Acquire firewall hardware and software.
3. Acquire firewall documentation, training,
and support.
4. Install firewall hardware and software.
5. Configure IP routing.
6. Configure firewall packet filtering.
7. Configure firewall logging and alert mechanisms.
8. Test the firewall system.
9. Install the firewall system.
10. Phase the firewall system into operation.
Extrait du cours deploying firewalls architecture firewall designs
Preface
This document is one of a series of publications of the Software Engineering Institute at Carnegie Mellon University called security improvement modules. They are intended to provide practical guidance to help organizations improve the security of their networked computer systems.
Module structure
Each module addresses an important but relatively narrowly defined problem in network and system security. The first section of the module describes the problem and outlines a set of security improvement practicesto help solve it. Each practice is a recommended way of performing common tasks related to the secure operation of networked computer systems. The remaining sections of the module are detailed descriptions of the practices. Each includes a rationale for the recommended actions and a description of how to perform them.
Intended audience
The practices are primarily written for system and network administrators whose day-to-day activities include installation, configuration, and maintenance of the computers and networks. Occasionally, practices are written to assist the managers responsible for network and system administration.
Acknowledgements
This report and the effort to produce it were sponsored by the USAF Embedded Computer Resources Support Improvement Program (ESIP). The authors are pleased to acknowledge LtCol Joseph Jarzombek for engaging as reviewers and collaborators the USAF Information Warfare Center (AFIWC) under Mr. Feliciano Rodriguez, Director, Engineering and Analysis. AFIWC assisted in the selection of the Security Improvement Module title and content. AFIWC provided expert review and recommendations. The authors believe that this collaboration resulted in a better module for ESIP, AFIWC, and the community as a whole.
The authors appreciate the support and cooperation of all AFIWC personnel that contributed to Deploying Firewalls. We would like to specifically recognize the individuals that we interfaced with: Feliciano Rodriguez, Jose Linero, Joe Cano, James Dennis, Lt Lynn Blankenship, and Lt Paul Townley.
Deploying Firewalls
A firewall is a combination of hardware and software used to implement a security policy governing the network traffic between two or more networks, some of which may be under your administrative control (e.g., your organization’s networks) and some of which may be out of your control (e.g., the Internet). A network firewall commonly serves as a primary line of defense against external threats to your organization’s computer systems, networks, and critical information. Firewalls can also be used to partition your organization’s internal networks, reducing your risk from insider attacks.Firewall technologies have entered into the mainstream. The “1999 Computer Security Institute/FBI Computer Crime and Security Survey” [Power 99] indicates that 91 percent of the organizations surveyed already deploy firewalls. Articles and other references covering evaluation, selection, and configuration of firewall technologies are now common in the popular press (see References at the end of this section).However, there has been little published about designing, installing, deploying, operating, and maintaining firewalls. The practices in this module will address designing, installing, and deploying firewalls.
1 Design the firewall system.
Designing a firewall requires that you understand and identify the boundaries between security domains in your network. A network security domain is a contiguous region of a network that operates under a single, uniform security policy. Wherever these domains intersect, there is a potential need for a policy conflict resolution mechanism at that boundary. This is where firewall technology can help.
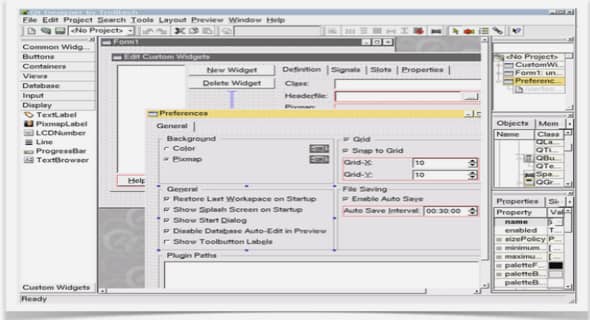
The most common boundary where firewalls are applied today is between an organization’s internal networks and the Internet. When establishing an Internet firewall, the first thing you must decide is its basic architecture (assuming you have previously established your firewall requirements and the security policy it is intended to implement). In this context, architecture refers to the inventory of components (hardware and software), and the connectivity and distribution of functions among them. There are two classes of firewall architectures, which we refer to as the single layerand the multiple layerarchitectures.
Why this is important
Your ability to enforce your organization’s security policies accurately can be severely impaired if you have not chosen an appropriate and effective firewall architecture. This design will determine which policies can and cannot be enforced, as well as how well the firewall will accomplish its objectives over time. Firewall architectures are difficult and expensive to change after deployment, so there is considerable value (cost savings) in creating an effective, scalable, and manageable design first.
Firewall systems provide a policy enforcement mechanism at a security domain boundary.
If an adversary can exploit another less protected boundary to gain access into your network (for example, a modem on a user workstation or via a partner’s network), then any firewall systems you have deployed on other boundaries to control access to that network will be ineffective.
……..
Deploying firewalls architecture firewall designs (1407 KO) (Cours PDF)