Sommaire: Support de cours securing desktop workstations
1. Develop a computer deployment plan that includes security issues.
2. Keep operating systems and applications software up to date.
3. Configure computers for user authentication.
4. Configure computer operating systems with appropriate object, device, and file access controls.
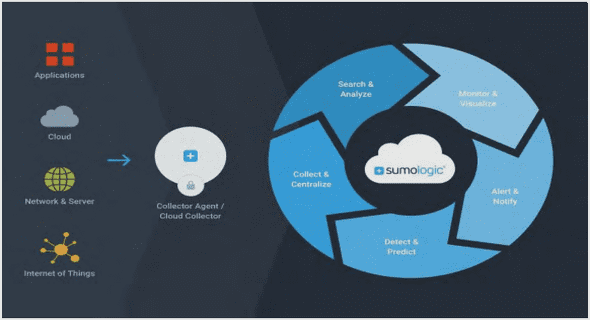
5. Identify and enable system and network logging mechanisms.
6. Configure computers for file backups.
7. Protect computers from viruses and similar programmed threats.
8. Configure computers for secure remote administration.
9. Configure computers to provide only selected network services.
10. Configure network service clients to enhance security.
11. Configure multiple computers using a tested model configuration and a secure replication procedure.
12. Allow only appropriate physical access to computers.
13. Develop and promulgate an acceptable use policy for workstations.
Extrait du support de cours securing desktop workstations
Develop a computer deployment plan that includes security issues.
Most deployment plans address the cost of the computers, schedules to minimize work disruption, installation of applications software, and user training. In addition, you need to include a discussion of security issues.
Why this is important
You can eliminate many networked systems vulnerabilities and prevent many security problems if you securely configure computers and networks before you deploy them. Vendors typically set computer defaults to maximize available functions so you usually need to change defaults to meet your organization’s security requirements.You are more likely to make decisions about configuring computers appropriately and consistently when you use a detailed, well-designed deployment plan. Developing such a plan will support you in making some of the hard trade-off decisions between usability and security.
Consistency is a key factor in security as it fosters predictable behavior. This will make it easier for you to maintain secure configurations and help you to identify security problems (which often manifest themselves as deviations from predictable, expected behavior).
Refer to the practice, “Keep operating systems and applications software up to date.”
How to do it
Make the decisions described below and then record them.
Note: We assume that you are deploying workstations and servers in an existing infrastructure, which includes an existing network. The security issues related to the network architecture, including where you place servers and workstations on the network, are outside the scope of this practice.
Policy considerations
Your organization’s security policy for networked systems should
• require that a detailed computer deployment plan be developed and followed whenever computers are being deployed (or redeployed)
• require that access to your deployment plan be permitted to only those who require the information to perform their jobs
Keep operating systems and applications software up to date.
You need to stay informed of vendors’ security-related updates to their products, which may be called updates, upgrades, patches, service packs, or hot fixes. Whenever an update is released, you need to evaluate it, determine if it is applicable to your organization’s computers, and, if so, install it.
Why this is important
Because software systems are so complex, it is common for security-related problems to be discovered only after the software has been in widespread use. Although most vendors try to address known security flaws in a timely manner, there is normally a gap from the time the problem is publicly known, the time the vendor requires to prepare the correction, and the time you install the update. This gap gives potential intruders an opportunity to take advantage of this flaw and mount an attack on your computers and networks. To keep this time interval as short as possible, you need to stay aware of
• announcements of security-related problems that may apply to your systems
• immediate steps you can take to reduce your exposure to the vulnerability, such as disabling the affected software
• permanent fixes from vendors
Configure computers for user authentication.
An organization’s security policy for networked systems should specify that only authorized users may access the computers. To enforce this, you need to configure the computer to authenticate a prospective user, who must prove that they are authorized for such access (securing desktop workstations).
Configuring the computer for authentication usually involves configuring parts of the operating system, firmware, and applications such as the software that implements a network service. If your organization has authentication servers, configuring a new workstation or network server for user authentication may require you to make configuration changes on another computer. In special cases, you may also use authentication hardware such as tokens, one-time password devices, or biometric devices (devices that can recognize a person based on biological haracteristics, such as fingerprints or patterns in retinal blood vessels).
……..
Support de cours securing desktop workstations (369 KO) (Cours PDF)